Iran Focus
London, 27 Dec – A new study is soon to be published by Collin Anderson and Karim Sadjadpour of the Carnegie Endowment for International Peace. It is called “Iran’s Cyber Threat” and it describes a country that, although not high on the cyber threat matrix, can still do considerable damage.
America and its allies exist in a dangerous electronic ecosystem. The media highlights Russia’s alleged hacking of the 2016 U.S. presidential campaign on a daily basis, but less attention is focused on the weapons available to dozens of smaller countries. With its relatively open systems, the US can be an easy target.
The Carnegie study describes a small Iranian cyber capability that evolved in part to gather foreign intelligence, as well as to spy on domestic opposition groups that came together in the 2009 Green Movement. After newspaper reports in 2012, regarding U.S. and Israeli “Stuxnet” malware attacks on the Iranian nuclear program that had started in 2007, Iranian hackers had payback motive, too.
The report notes that around 10 years ago, Iran’s home-grown hacking culture emerged. “Iran’s cyber capabilities appear to be indigenously developed, arising from local universities and hacking communities,” it says, and adds, “Threat actors seemingly arise from nowhere and operate in a dedicated manner until campaigns dissipate, often due to their discovery by researchers.”
A group calling itself the Iranian Cyber Army defaced dissident Twitter accounts in 2009, followed by websites belonging to the Voice of America. According to the Carnegie study, in 2011, an Iranian hacker penetrated a Dutch security firm called DigiNotar, and opened Gmail users in Iran to government surveillance.
In April 2012, malware known as “Flame” and “Wiper” hit Iran’s oil industry. A counterattack was launched by Iranians in August 2012 against the Saudi Aramco oil company, using a wiper virus known as “Shamoon.” The Carnegie researchers says that the attack affected tens of thousands of Saudi Aramco computers and caused tens or even hundreds of millions of dollars in damage.
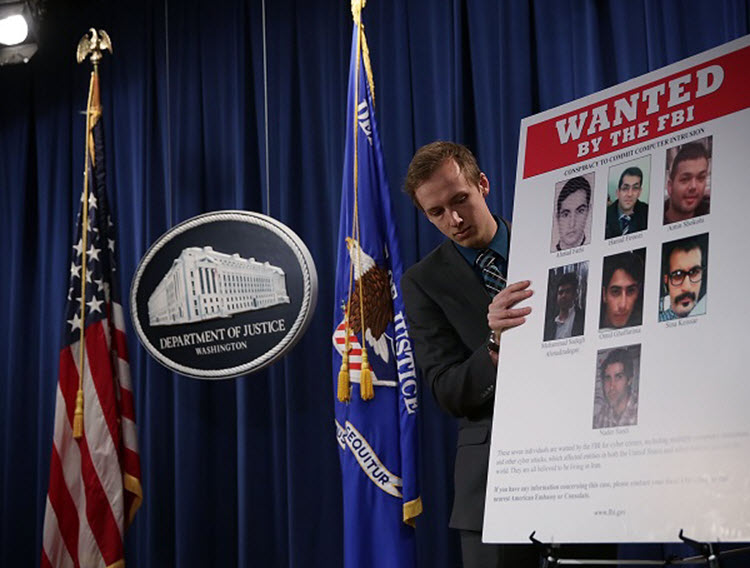
Iran also attacked the U.S. in September 2012. A hacker group calling itself the Izz ad-Din al-Qassam Cyber Fighters began attacking U.S. banks and financial institutions with “distributed denial of service,” or DDoS, which floods targeted computers with so much traffic that their systems crash. Though unsophisticated, this is a surprisingly effective strategy. In fact, the FBI concluded that from 2012 to 2013, the Iranian operation “locked hundreds of thousands of banking customers out of accounts for long periods of time and resulted in tens of millions of costs to remediate,” according to the Carnegie analysts.
The Carnegie reports cites an NSA assessment that “indicates that these attacks are in retaliation to Western activities against Iran’s nuclear sector and that senior officials in the Iranian government are aware of these attacks.”
Recently, a website called “The Cipher Brief,” which focuses on intelligence issues, claimed, “Iran’s . . . Cyber Hackers Poised to Strike If Trump Shreds Nuke Deal.”
This month, the computer security firm, FireEye, reported that a group of Iranian hackers, dubbed “APT34,” have developed a new backdoor cyber-surveillance technique.
Cyber security should be an important objective for the US in the coming year.


